Our Mission
Social media has undergone a major transformation
Partners
We are partners with industry leaders
Customers
Updating brand assets across accounts is a nightmare.
Our Mission
Social media has undergone a major transformation
Partners
We are partners with industry leaders
Customers
Updating brand assets across accounts is a nightmare.
Our Mission
Social media has undergone a major transformation
Partners
We are partners with industry leaders
Customers
Updating brand assets across accounts is a nightmare.
How to Conduct an Enterprise Social Media Impersonation Audit
How to Conduct an Enterprise Social Media Impersonation Audit
Learn how to audit your brand for social media impersonation. Identify fake accounts and protect your reputation with this step-by-step guide.

Bill Roberts
Founder

Quick Summary
Your brand likely has dozens of impersonator accounts operating right now. Some are dormant. Others are actively running phishing scams, selling counterfeits, or harvesting customer credentials using your logo and voice. This guide walks through the systematic process of finding these accounts.
Your Brand Has Impostors
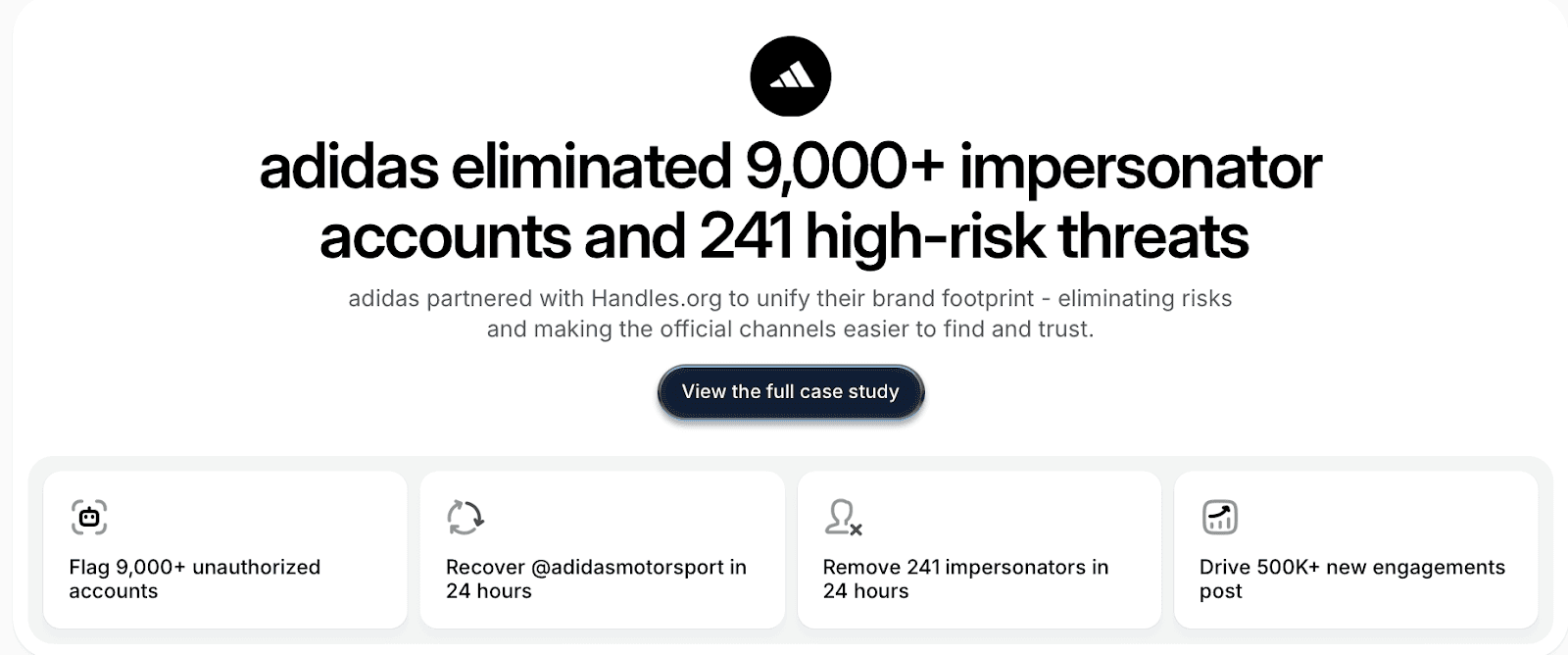
Handles identified over 9,000 impersonator accounts threatening a single enterprise client. The client's internal team had found 47.
That gap exists because impersonators operate faster than manual processes can track. A fake account costs nothing to create and takes minutes to launch. By the time your team runs a quarterly audit, scammers have already copied your logo, mimicked your bio, and started DMing your customers with phishing links.
The framework below will help you find impersonators, prioritize threats, execute takedowns, and prevent recurrence. But we'll be direct about something throughout: the manual version of this process has fundamental limitations that are very difficult to overcome.
Why Listen to Us
Handles pioneered social-first infrastructure for brands like Adidas, Framer, and Cohere.
We're the first company with direct platform partnerships, focusing exclusively on social media rather than trademarks or web assets. We've audited thousands of accounts and built governance systems that prevent breaches before they happen.
What Is a Social Media Impersonation Audit?
An impersonation audit systematically searches social networks for fake accounts, pages, and profiles that replicate your brand, executives, or products. The goal is to find them, prioritize them by threat level, and remove them.
Impersonation takes several forms:
Direct brand impersonation: Exact name and logo usage
Executive impersonation: Fake CEO or leadership profiles, often supporting business email compromise scams
Product/sub-brand impersonation: Targeting specific offerings
Typosquatting: Misspelled versions of your handles
Visual impersonation: Your imagery without explicitly claiming to be you
Verification offers limited protection here. Badges are available for main accounts only, not regional pages, sub-brands, or executive profiles. Platform detection systems don't monitor across networks, so you need separate processes for each platform. And impersonators move fast.
Scam accounts can go live, cause damage, and disappear within hours. Platforms tend to prioritize political disinformation over brand protection, so response times vary wildly.
The 7-Phase Social Media Impersonation Audit
Phase 1: Map Your Legitimate Brand Presence
Before hunting fakes, you need to document reality. This step sounds obvious, but it's where most audits already start failing. Enterprise brands consistently underestimate how many official accounts they actually operate.
Start by listing every main brand account across all platforms, then expand to include:
Country and market-specific accounts (@BrandUSA, @BrandUK)
Sub-brands and product-specific accounts
Executive social profiles (CEO, CMO, founders)
Employee advocacy profiles
Approved partner and affiliate accounts
Archived accounts you still control
For each account, document the platform, handle, verification status, primary contact or manager, launch date, and official imagery being used.
This inventory matters because you cannot recognize impostors without a complete picture of what's real. We routinely find that brands discover more official accounts than they knew existed during this phase. That's a problem. If your own team doesn't know which accounts are legitimate, impersonators have already won half the battle.
⚠️ Manual limitation: Keeping this inventory current requires constant maintenance. Accounts get created for campaigns and forgotten. Employees leave and take institutional knowledge with them. Spreadsheet-based tracking becomes outdated within weeks.
Phase 2: Search Systematically Across Platforms
Manual impersonator hunting requires platform-by-platform searches using multiple query variations. Start with your exact brand name, then expand:
Add suffixes: official, HQ, support, real
Add locations: USA, UK, NYC, your key markets
Try typosquatting: letter swaps, common misspellings
Test phonetic alternatives: YourBrand vs YurBrand
Add special characters: underscores, dashes, periods
Append numbers: YourBrand1, YourBrand2023
Search product names and executive names separately
Run these searches across Facebook (pages and profiles), Instagram (profiles and business accounts), LinkedIn (company pages and individual profiles), X, TikTok, YouTube, Pinterest, Threads, Reddit, Telegram, and WhatsApp. For brands operating internationally, use a VPN to search from different regions and check local platforms like WeChat and VK.
For each suspicious account, document:
URL and handle
Follower count
Creation date (if visible)
Content posting frequency
Contact information displayed
⚠️ Manual limitation: This process takes 4-8 hours for a thorough sweep. Impersonators can create new accounts in that same window. A single human searcher also can't match the pattern recognition that catches sophisticated impersonators using slight visual modifications or non-obvious name variations. Platform search algorithms don't surface every result, so manual queries miss accounts that algorithmic scanning catches.
Phase 3: Assess and Prioritize Threat Levels
Not all impersonators pose equal risk. Triage by potential harm.
Priority | Response Time | Examples |
High | Immediate | Active scams (fake giveaways, phishing), fake customer service harvesting credentials, misinformation with large following, exact visual matches, executive impersonation supporting BEC |
Medium | Within 2 weeks | Dormant accounts using brand imagery, partial visual similarities, 1K-10K followers, confusing parody accounts, counterfeit sellers |
Low | Monitor only | Obvious fan/parody accounts, small dormant accounts (<100 followers), accounts in non-operating markets |
Score each account from 1-10 based on deception depth, activity level, follower reach, scam indicators, and platform response likelihood.
⚠️ Manual limitation: Threat levels change. A dormant account can activate overnight. A small account can suddenly gain followers through paid promotion. Manual audits capture a point-in-time snapshot, not continuous risk assessment. By the time you've triaged your list, the highest-risk accounts may have already shifted.
Phase 4: Capture Evidence Systematically
Platform takedown requests require evidence, so document everything before taking action. For each impersonator, capture:
Full screenshots of profile (picture, bio, banner)
Posts misusing your brand
Visible links and handles
Date, timestamp, follower count, verification status
Harmful content (scam offers, fake promotions)
Customer complaints if visible
Archive profiles using Archive.today when possible. Organize with platform folders containing per-account subfolders, and maintain a spreadsheet linking evidence to entries.
Capture screenshots before sending takedown requests. Accounts routinely delete incriminating content once alerted to scrutiny.
Phase 5: Execute Platform Takedown Requests
Each platform handles impersonation reports differently:
Platform | How to Report | Response Time |
Facebook/Instagram | "Report Page/Account" → "Pretending To Be Me." For trademarks, use Meta's IP Help Center | 24-72 hours |
"Report this page" dropdown for company pages, "Report/Block" for profiles. Use Impersonation Form for trademarks | 48-96 hours | |
X | Report → "They're impersonating another person." Trademark holders use trademark policy form | 24 hours to 2 weeks |
TikTok | Profile → share arrow → Report → Report account → "Pretending to be someone" | Varies |
YouTube | Information tab → Impersonation. Use trademark complaint process for trademark claims | 1-2 weeks |
To improve success rates, submit reports from verified accounts when possible, include trademark registration numbers, cite specific policy violations, attach multiple screenshots, and follow up on stalled requests.
⚠️ Manual limitation: Platform response times vary from 24 hours to never. Persistence helps, but even persistent follow-up can't guarantee action. Handles' direct platform partnerships provide escalation paths that aren't available through standard reporting channels.
Phase 6: Monitor for Repeat Offenders
Impersonators return. After a successful takedown, the same bad actor often creates a new account within days.
Watch for patterns: similar handles (@FakeBrand becomes @FakeBrand_Official), reused profile images, identical bio text, same website links, consistent posting times. Set up Google Alerts for brand name mentions and enable social platform notifications where available.
Document all takedowns with enough detail to identify when the same actor creates new accounts. When patterns emerge showing repeat offenders, the situation moves into legal territory: trademark infringement filings, cease and desist letters, and cybercrime reports become appropriate responses.
⚠️ Manual limitation: Monitoring for repeat offenders requires constant vigilance. Human attention spans aren't designed for continuous monitoring across dozens of search variations. This is precisely where automated systems provide the most value.
Phase 7: Establish Ongoing Monitoring
Impersonation protection isn't a one-time project. Establish a maintenance cadence:
Weekly: Quick scans of critical platforms
Monthly: Comprehensive cross-platform searches
Quarterly: Full audits with breach simulations
Event-driven: Additional monitoring during launches, crises, and campaigns
Create an internal escalation process where customer service routes impersonator reports to brand protection, social media managers flag suspicious accounts immediately, and executive assistants monitor for leadership impersonation.
Track metrics to measure effectiveness:
Metric | Target |
Time-to-detect new impersonators | < 24 hours |
Time-to-takedown | < 72 hours |
Repeat offender rate | Trending down |
Customer-reported scams | Decreasing over time |
⚠️ Manual limitation: Everything described in this phase is theoretically achievable through manual effort. In practice, manual monitoring degrades over time.
The brands that maintain effective impersonation protection at scale have automated the detection and monitoring components, reserving human judgment for threat assessment and response decisions.
How Handles Simplifies Impersonation Audits
The manual process described above works… but we built Handles because we saw that manual processes fail at enterprise scale in predictable ways.
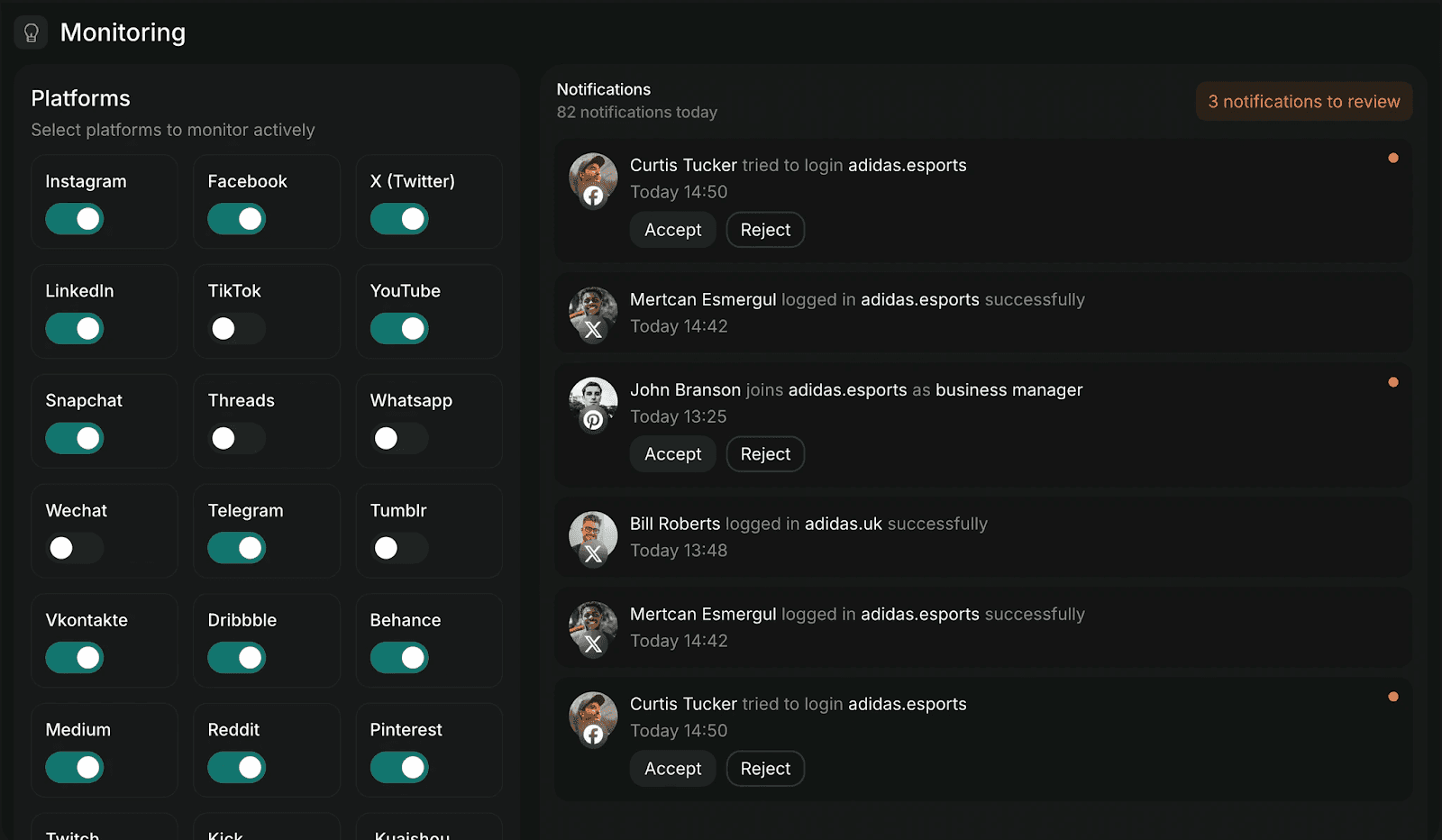
Handles uses AI to continuously monitor social platforms, detecting impersonators through visual recognition, text analysis, and behavioral patterns. The system catches sophisticated fakes that manual searches miss because it processes more search variations, recognizes subtle visual modifications, and operates continuously rather than in periodic sweeps.
Risk scoring automatically prioritizes threats, flagging active scams and high-deception accounts before dormant low-risk accounts. Direct platform partnerships enable faster takedowns through official escalation paths that standard reporting channels can't access.
The 9,000-impersonator case study represents what automated detection finds that manual audits miss. That client wasn't negligent. They had a brand protection process. The scale gap exists because manual processes can't match algorithmic scanning for coverage, speed, or consistency.
Protect Your Brand from Imposters
Impersonation damages brand trust and exposes customers to scams. The process in this guide will help you find and remove fake accounts. It will also reveal why manual approaches struggle to keep pace with impersonators who operate faster than periodic audits can track.
Start with Phase 1 and document your legitimate presence. Then hunt for fakes systematically. Or explore how Handles automates detection and takedowns at the scale enterprise brands require.
Get started withHandles and apply for abeta audit here.
Quick Summary
Your brand likely has dozens of impersonator accounts operating right now. Some are dormant. Others are actively running phishing scams, selling counterfeits, or harvesting customer credentials using your logo and voice. This guide walks through the systematic process of finding these accounts.
Your Brand Has Impostors
Handles identified over 9,000 impersonator accounts threatening a single enterprise client. The client's internal team had found 47.
That gap exists because impersonators operate faster than manual processes can track. A fake account costs nothing to create and takes minutes to launch. By the time your team runs a quarterly audit, scammers have already copied your logo, mimicked your bio, and started DMing your customers with phishing links.
The framework below will help you find impersonators, prioritize threats, execute takedowns, and prevent recurrence. But we'll be direct about something throughout: the manual version of this process has fundamental limitations that are very difficult to overcome.
Why Listen to Us
Handles pioneered social-first infrastructure for brands like Adidas, Framer, and Cohere.
We're the first company with direct platform partnerships, focusing exclusively on social media rather than trademarks or web assets. We've audited thousands of accounts and built governance systems that prevent breaches before they happen.
What Is a Social Media Impersonation Audit?
An impersonation audit systematically searches social networks for fake accounts, pages, and profiles that replicate your brand, executives, or products. The goal is to find them, prioritize them by threat level, and remove them.
Impersonation takes several forms:
Direct brand impersonation: Exact name and logo usage
Executive impersonation: Fake CEO or leadership profiles, often supporting business email compromise scams
Product/sub-brand impersonation: Targeting specific offerings
Typosquatting: Misspelled versions of your handles
Visual impersonation: Your imagery without explicitly claiming to be you
Verification offers limited protection here. Badges are available for main accounts only, not regional pages, sub-brands, or executive profiles. Platform detection systems don't monitor across networks, so you need separate processes for each platform. And impersonators move fast.
Scam accounts can go live, cause damage, and disappear within hours. Platforms tend to prioritize political disinformation over brand protection, so response times vary wildly.
The 7-Phase Social Media Impersonation Audit
Phase 1: Map Your Legitimate Brand Presence
Before hunting fakes, you need to document reality. This step sounds obvious, but it's where most audits already start failing. Enterprise brands consistently underestimate how many official accounts they actually operate.
Start by listing every main brand account across all platforms, then expand to include:
Country and market-specific accounts (@BrandUSA, @BrandUK)
Sub-brands and product-specific accounts
Executive social profiles (CEO, CMO, founders)
Employee advocacy profiles
Approved partner and affiliate accounts
Archived accounts you still control
For each account, document the platform, handle, verification status, primary contact or manager, launch date, and official imagery being used.
This inventory matters because you cannot recognize impostors without a complete picture of what's real. We routinely find that brands discover more official accounts than they knew existed during this phase. That's a problem. If your own team doesn't know which accounts are legitimate, impersonators have already won half the battle.
⚠️ Manual limitation: Keeping this inventory current requires constant maintenance. Accounts get created for campaigns and forgotten. Employees leave and take institutional knowledge with them. Spreadsheet-based tracking becomes outdated within weeks.
Phase 2: Search Systematically Across Platforms
Manual impersonator hunting requires platform-by-platform searches using multiple query variations. Start with your exact brand name, then expand:
Add suffixes: official, HQ, support, real
Add locations: USA, UK, NYC, your key markets
Try typosquatting: letter swaps, common misspellings
Test phonetic alternatives: YourBrand vs YurBrand
Add special characters: underscores, dashes, periods
Append numbers: YourBrand1, YourBrand2023
Search product names and executive names separately
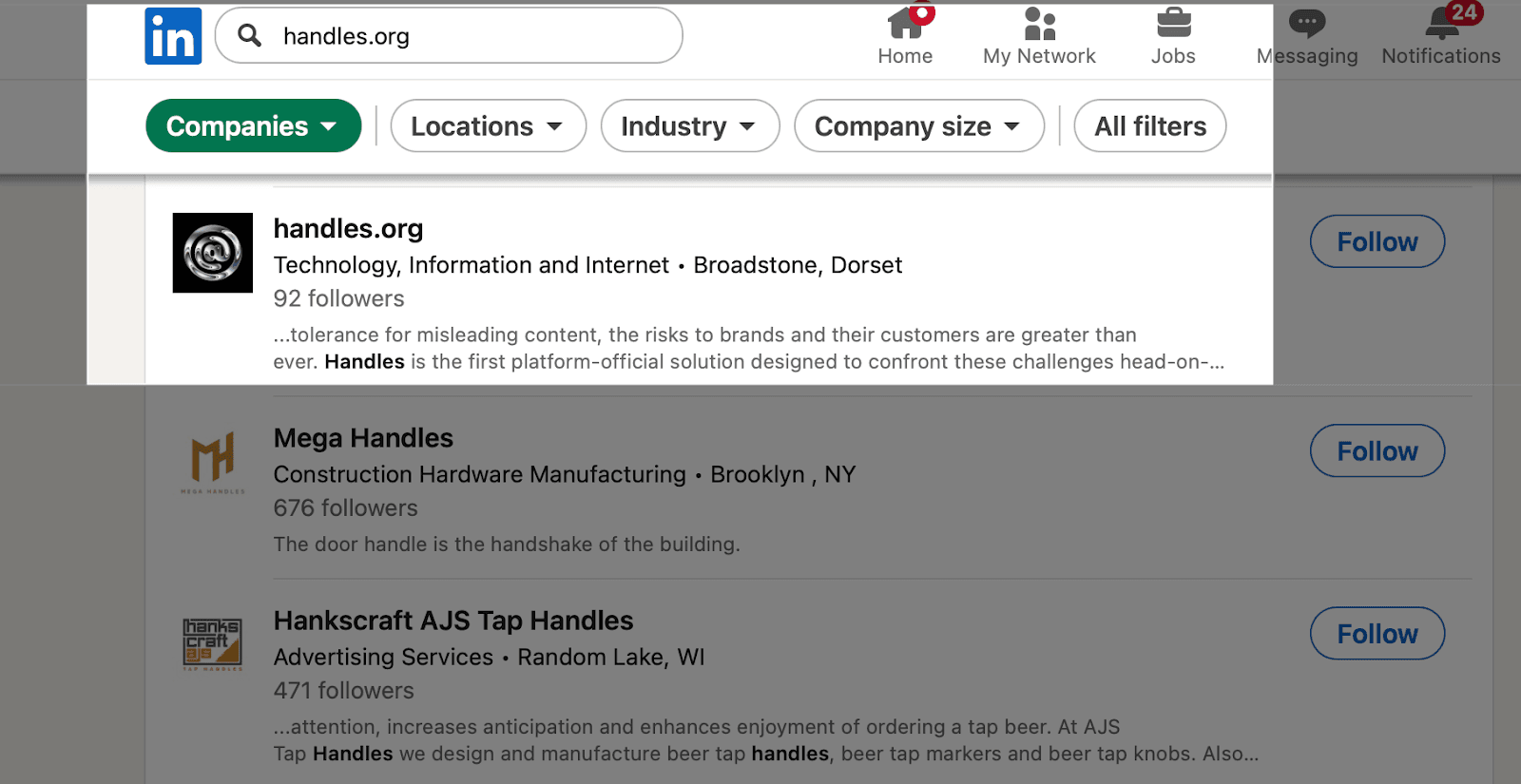
Run these searches across Facebook (pages and profiles), Instagram (profiles and business accounts), LinkedIn (company pages and individual profiles), X, TikTok, YouTube, Pinterest, Threads, Reddit, Telegram, and WhatsApp. For brands operating internationally, use a VPN to search from different regions and check local platforms like WeChat and VK.
For each suspicious account, document:
URL and handle
Follower count
Creation date (if visible)
Content posting frequency
Contact information displayed
⚠️ Manual limitation: This process takes 4-8 hours for a thorough sweep. Impersonators can create new accounts in that same window. A single human searcher also can't match the pattern recognition that catches sophisticated impersonators using slight visual modifications or non-obvious name variations. Platform search algorithms don't surface every result, so manual queries miss accounts that algorithmic scanning catches.
Phase 3: Assess and Prioritize Threat Levels
Not all impersonators pose equal risk. Triage by potential harm.
Priority | Response Time | Examples |
High | Immediate | Active scams (fake giveaways, phishing), fake customer service harvesting credentials, misinformation with large following, exact visual matches, executive impersonation supporting BEC |
Medium | Within 2 weeks | Dormant accounts using brand imagery, partial visual similarities, 1K-10K followers, confusing parody accounts, counterfeit sellers |
Low | Monitor only | Obvious fan/parody accounts, small dormant accounts (<100 followers), accounts in non-operating markets |
Score each account from 1-10 based on deception depth, activity level, follower reach, scam indicators, and platform response likelihood.
⚠️ Manual limitation: Threat levels change. A dormant account can activate overnight. A small account can suddenly gain followers through paid promotion. Manual audits capture a point-in-time snapshot, not continuous risk assessment. By the time you've triaged your list, the highest-risk accounts may have already shifted.
Phase 4: Capture Evidence Systematically
Platform takedown requests require evidence, so document everything before taking action. For each impersonator, capture:
Full screenshots of profile (picture, bio, banner)
Posts misusing your brand
Visible links and handles
Date, timestamp, follower count, verification status
Harmful content (scam offers, fake promotions)
Customer complaints if visible
Archive profiles using Archive.today when possible. Organize with platform folders containing per-account subfolders, and maintain a spreadsheet linking evidence to entries.
Capture screenshots before sending takedown requests. Accounts routinely delete incriminating content once alerted to scrutiny.
Phase 5: Execute Platform Takedown Requests
Each platform handles impersonation reports differently:
Platform | How to Report | Response Time |
Facebook/Instagram | "Report Page/Account" → "Pretending To Be Me." For trademarks, use Meta's IP Help Center | 24-72 hours |
"Report this page" dropdown for company pages, "Report/Block" for profiles. Use Impersonation Form for trademarks | 48-96 hours | |
X | Report → "They're impersonating another person." Trademark holders use trademark policy form | 24 hours to 2 weeks |
TikTok | Profile → share arrow → Report → Report account → "Pretending to be someone" | Varies |
YouTube | Information tab → Impersonation. Use trademark complaint process for trademark claims | 1-2 weeks |
To improve success rates, submit reports from verified accounts when possible, include trademark registration numbers, cite specific policy violations, attach multiple screenshots, and follow up on stalled requests.
⚠️ Manual limitation: Platform response times vary from 24 hours to never. Persistence helps, but even persistent follow-up can't guarantee action. Handles' direct platform partnerships provide escalation paths that aren't available through standard reporting channels.
Phase 6: Monitor for Repeat Offenders
Impersonators return. After a successful takedown, the same bad actor often creates a new account within days.
Watch for patterns: similar handles (@FakeBrand becomes @FakeBrand_Official), reused profile images, identical bio text, same website links, consistent posting times. Set up Google Alerts for brand name mentions and enable social platform notifications where available.
Document all takedowns with enough detail to identify when the same actor creates new accounts. When patterns emerge showing repeat offenders, the situation moves into legal territory: trademark infringement filings, cease and desist letters, and cybercrime reports become appropriate responses.
⚠️ Manual limitation: Monitoring for repeat offenders requires constant vigilance. Human attention spans aren't designed for continuous monitoring across dozens of search variations. This is precisely where automated systems provide the most value.
Phase 7: Establish Ongoing Monitoring
Impersonation protection isn't a one-time project. Establish a maintenance cadence:
Weekly: Quick scans of critical platforms
Monthly: Comprehensive cross-platform searches
Quarterly: Full audits with breach simulations
Event-driven: Additional monitoring during launches, crises, and campaigns
Create an internal escalation process where customer service routes impersonator reports to brand protection, social media managers flag suspicious accounts immediately, and executive assistants monitor for leadership impersonation.
Track metrics to measure effectiveness:
Metric | Target |
Time-to-detect new impersonators | < 24 hours |
Time-to-takedown | < 72 hours |
Repeat offender rate | Trending down |
Customer-reported scams | Decreasing over time |
⚠️ Manual limitation: Everything described in this phase is theoretically achievable through manual effort. In practice, manual monitoring degrades over time.
The brands that maintain effective impersonation protection at scale have automated the detection and monitoring components, reserving human judgment for threat assessment and response decisions.
How Handles Simplifies Impersonation Audits
The manual process described above works… but we built Handles because we saw that manual processes fail at enterprise scale in predictable ways.
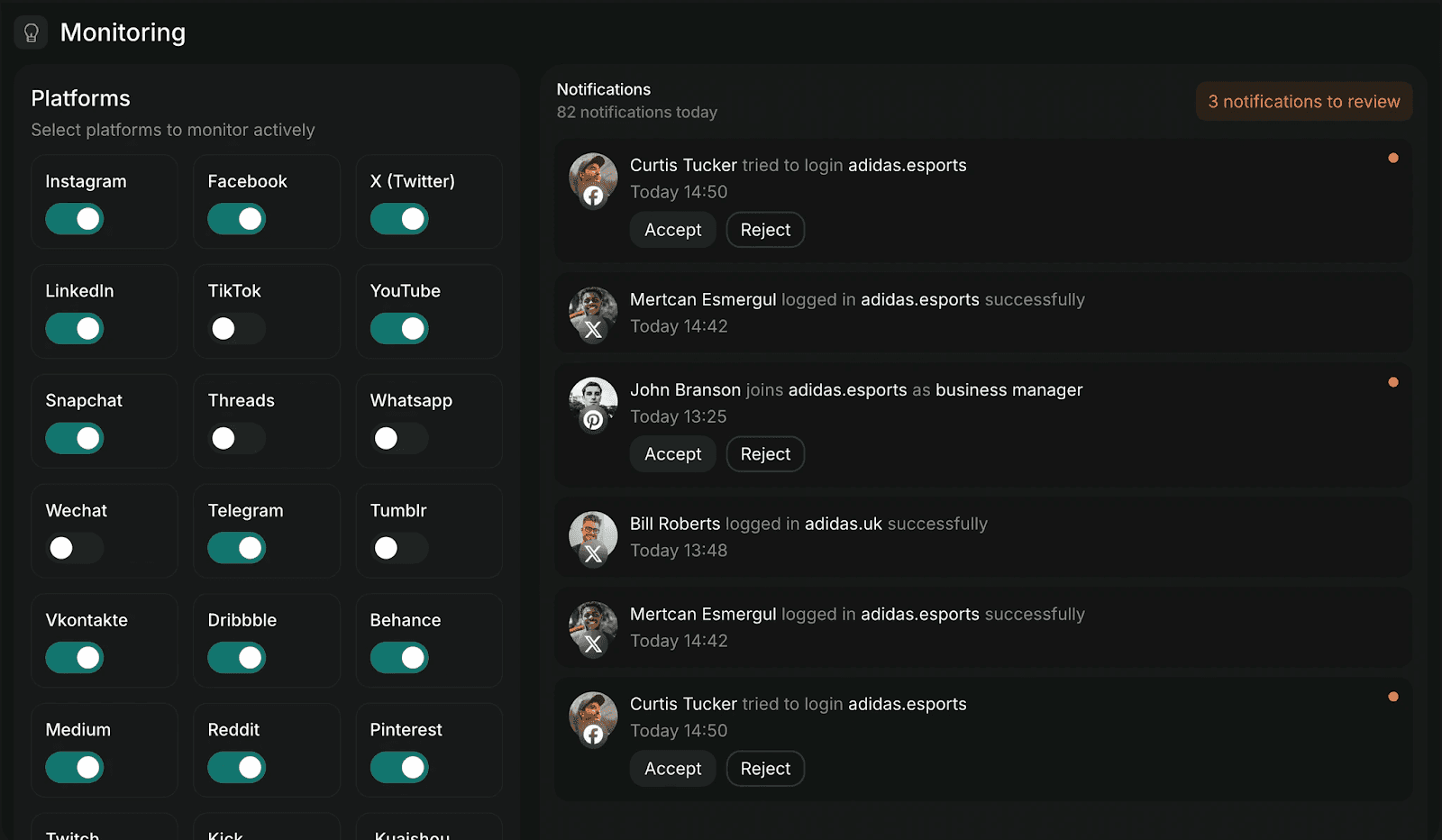
Handles uses AI to continuously monitor social platforms, detecting impersonators through visual recognition, text analysis, and behavioral patterns. The system catches sophisticated fakes that manual searches miss because it processes more search variations, recognizes subtle visual modifications, and operates continuously rather than in periodic sweeps.
Risk scoring automatically prioritizes threats, flagging active scams and high-deception accounts before dormant low-risk accounts. Direct platform partnerships enable faster takedowns through official escalation paths that standard reporting channels can't access.
The 9,000-impersonator case study represents what automated detection finds that manual audits miss. That client wasn't negligent. They had a brand protection process. The scale gap exists because manual processes can't match algorithmic scanning for coverage, speed, or consistency.
Protect Your Brand from Imposters
Impersonation damages brand trust and exposes customers to scams. The process in this guide will help you find and remove fake accounts. It will also reveal why manual approaches struggle to keep pace with impersonators who operate faster than periodic audits can track.
Start with Phase 1 and document your legitimate presence. Then hunt for fakes systematically. Or explore how Handles automates detection and takedowns at the scale enterprise brands require.
Get started withHandles and apply for abeta audit here.
Social media governance
& Infrastructure.
Social media governance
& Infrastructure.

© 2026 Handles.ai. All Rights Reserved.




